How to: Document Active Directory
BY IT GLUE | July 27, 2016
Active Directory (AD), is the foundation to your clients’ network authentication. The key to security grouping, application access, email address book, file replication, wireless access, VPN, and more. Do you think it is worthwhile to ensure it is documented accurately for every environment you support? You bet it is.
Simple
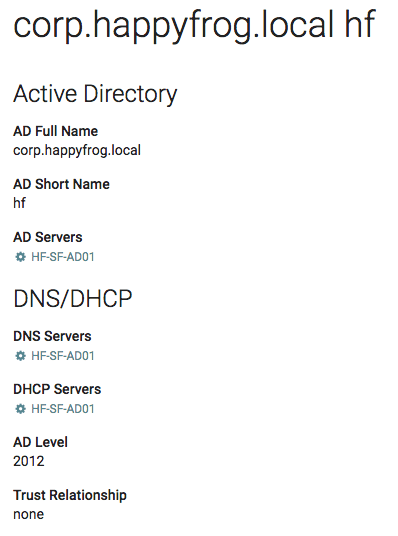
The included template within IT Glue™ is simple, in fact deliberately simple. AD is so central to so many systems, that you need the information to be easy, accurate, complete and linked to every context in which you need it. From a support perspective 90% of what you do with Active Directory is find a Domain Controller, log on remotely, add/move/change something, or to troubleshoot an issue. Here are the essentials to document in AD:
- Domain full and short names
- All domain controllers
- Roles: DNS, DHCP
- Linked credentials one click away
Available
Your typical workflow as a client user calls in: click Active Directory, click through to the Server, click Manage to open the server in your RMM tool, click the credentials for AD admin and copy across. That’s 4 clicks and a password copy and you are troubleshooting, knowing that the data is accurate.
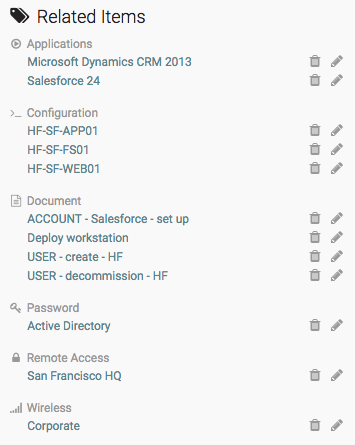
Now you have these simple details recorded, let’s release them to be incredibly useful. Link every aspect of the infrastructure that requires AD authentication: applications, wireless devices, VPN, file servers, web servers, app servers. Now consider all procedural documentation that will require AD to complete. New user setup docs, decommissioning docs, application user account configuration, troubleshooting docs. Of course this list of related items can grow quite quickly, so consider the most often used documentation. You may wish to apply the 80-20 rule here – 80% of your client issues are likely to be addressed by 20% of their documentation! If the Related Items pane in your Active Directory asset doesn’t look something like this, you’re missing some significant efficiency gains with your team:
Ideas for further development
More fields – once you’ve completed documenting AD to the level above for every client, you might consider adding more information into the Active Directory Flexible Asset. Operational Units and the vision for their use, replication schedules between sites, federation to Azure, SSO SAML connections to applications like IT Glue, standard fields required for the Address Book.
Security Groups – in many ways, Active Directory (AD), is its own documentation, and to re-produce the details outside the AD servers themselves would end up in unnecessary duplication of information, and can quickly create two versions of ‘the truth’. However in the KB article “Security groups – document for authorization” we suggest a very simple approach to keeping a separate record of security groups. They can be linked to documents, applications and other flexible assets, and give you an excellent place to collaborate with your clients visibly on security groups.
Group Policy – in a similar manner, Group Policy can benefit from a quick reference document to capture your standard GPO policies – e.g. firewall lock down, access to printers and shared drives, restrictions of control panel settings, password complexity. Your needs will vary so much in this area, it’s tough to suggest a Flexible Asset design for you. We’d love you to share your designs with the community.
Auto-update Active Directory password
Since this How To article was written, we’ve added the ability to auto-update Active Directory passwords in IT Glue, using our integration with QuickPass. For more details on this integration, click here.
Happy Documenting, from the #GlueCrew!
| How to Home | ← How to Manage Domains and SSL Certificates | How to Document a LAN → |